Unomaly algorithmically analyzes log structures and frequency to identify anomalies

Profile events from log structures
Identifies recurring patterns in structures, source and frequency

Flag anomalous events
Alerts when new events don’t fit established patterns

Cluster events into situations
Creates time-based groupings of anomalies to spur investigations
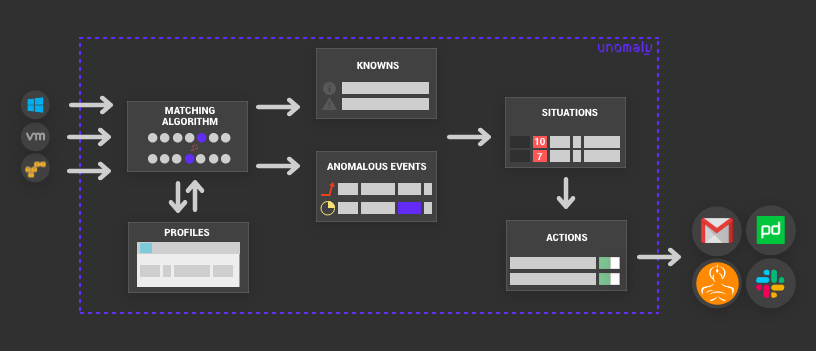
How Unomaly Works
Unomaly establishes a baseline of your entire infrastructure and starts alerting you to the changes in your deployment after a couple of days
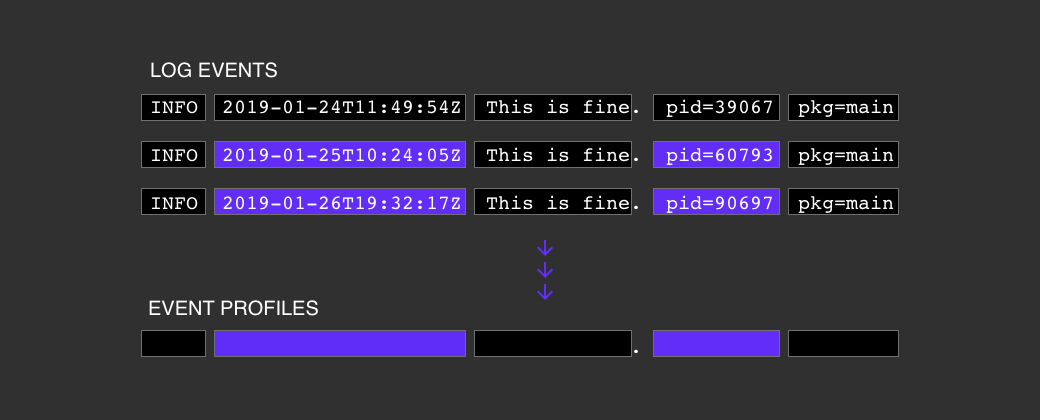
Profile events from log structures
As log events stream in, Unomaly records a profile for each log event with information about the event’s structure, sources, frequency patterns and intervals. Each collection of profiles describes the baseline for a log source in your environment.
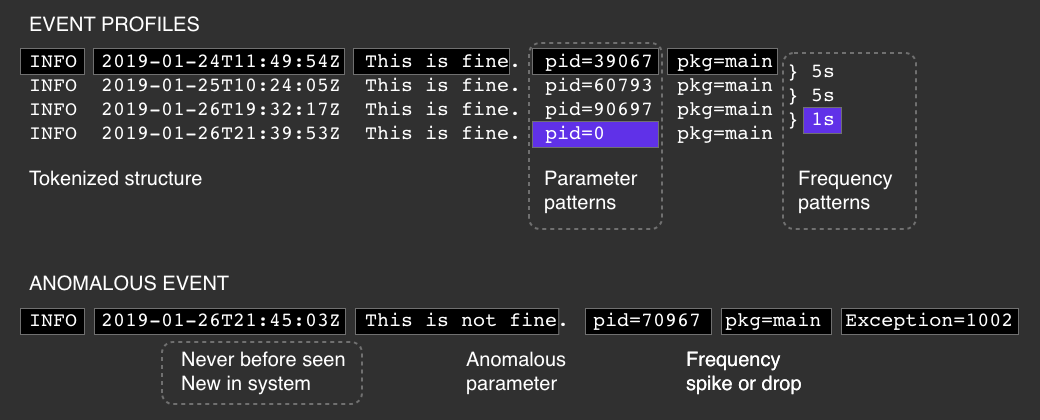
Training completes after a couple of days, but analysis and learning continues as long as Unomaly receives additional data.
During analysis of a log event's structure, similar profiles are merged into one aggregated profile with dynamic parameters. Because the majority of log events have the same or similar structure, this merging process reduces the amount of data to analyze by at least 99%.
Flag anomalous events
Unomaly determines whether incoming log events are different from previously seen profiles, first based on their structure and then based on other criteria: dynamic parameters and frequency patterns.
Types of anomalies:
Structural
Events that do not fit into established patterns of log structures.
Parameter
Unique values occur within an previously identified event profile
Frequency
Increases or decreases of the rhythm of a an event.
Cluster anomalies into actionable situations
When anomalous events occur within a rolling 60 second window on a single log source, Unomaly clusters them together into a situation. Situations receive a score that is based on the type and number of anomalies.
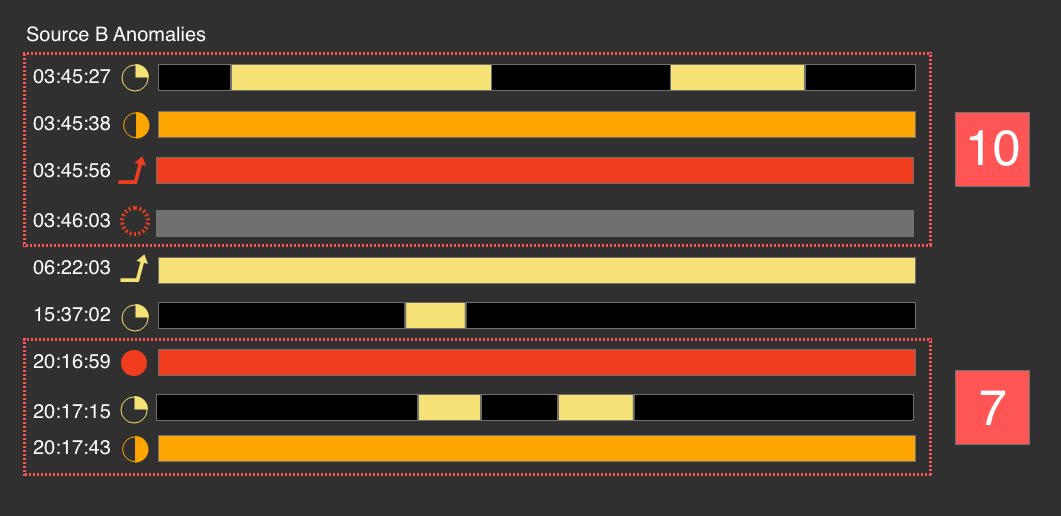
Situations are tracked per log source to immediately see the health of that system to start your investigations. Drilling down into the individual anomalies that are part of the situation and surrounding event profiles will provide additional context.
Dive deeper into how Unomaly works in our product documentation.
Core beliefs in our technology
Universal Data Tokenization
All log data must be analyzed without concern for source, structure or format because it is the most context-rich information about your environment and the only way to have a complete view.
Rapid Progressive Learning
Unomaly must stay up-to-date and relevant within our customers’ ever-evolving data centers, therefore we update our models of your data as new logs arrive.
Data Privacy and Integrity
Working with data comes with responsibility. Unomaly was built from the ground up with privacy and compliance in mind. As Unomaly reduces data we only keep what is important to help you avoid harboring sensitive data.
Data Reduction Pipeline
You should have full visibility but only need to review a fraction of the data. Unomaly is designed to reduce repeating data to protect your infrastructure and team from the spikes and burdens of scale.
Multi-type Anomaly Detection
Many factors make data anomalous. Unomaly takes this into account and is designed to detect different types of anomalies in real-time to paint a complete picture of every issue.
Flexible and Self-managing
Software systems should not need continuous maintenance. Unomaly deploys close to where you run your software, automates analysis and effectively reduces data algorithmically.